
Third-Party Assessment
Trust, but Verify
Your organisation’s security isn’t just about your own systems; it also depends on every vendor, contractor, or partner you work with. You wouldn’t hand the keys to your office to someone without knowing who they are, what they need access to, and when those keys are returned. Yet digitally, many organisations do exactly that.
Forgotten accounts, weak controls, or insecure tools can create hidden backdoors that put your data, systems, and reputation at risk. We help you identify, manage, and reduce these risks, from vendor selection and reviewing software connections to access control. We focus on what's important for your organisation.
Why Third-Party Risk Matters
A lot of cyber incidents don’t start with a direct attack on your organisation. They start somewhere else. A vendor with weak security. A contractor whose access was never removed. A software tool that has more permissions than it needs.
Because third parties often sit outside your direct control, their risks are easy to overlook, until they become your problem. Without proper oversight, third-party access can lead to:
- Data breaches through trusted vendors
- Unauthorised or forgotten access of contractors
- Supply-chain attacks via connected software
- Compliance issues during audits or incidents
Third-party risk management isn’t about distrust. It’s about visibility, control, and accountability, without slowing down your business.
Security at every stage
Insights
Secure Mapping
We assess your current setup to reveal hidden risks by mapping which third-party users, tools, APIs, and software access your data.
Assessment
Shop with Confidence
We check to make sure the security standards of new vendors and new software align with yours before contracts are signed.
Management
Continuous Vigilance
We give you the tools for safe third-party offboarding, recurring audits, and ongoing monitoring to keep digital backdoors closed.
Turning Third-Party risk into verified trust
From tangled web to
total transparency
You can choose to focus on the areas that matter most to your organisation, or let us assess your entire third-party landscape. With this approach, you gain confidence that your third-party relationships are secure, controlled, and aligned with your policies, without being forced into a one-size-fits-all solution.
Access Overview
Mapping of every vendor, partner, and tool connected to your systems, giving you a clear overview of who has access to your data.
Secure Vetting
Evaluation of new vendors by custom questionnaires, so that you can verify their security before they enter your environment.
Access Control
Guidance on onboarding and offboarding with least-privilege principles, ensuring external parties only have access to what they need.
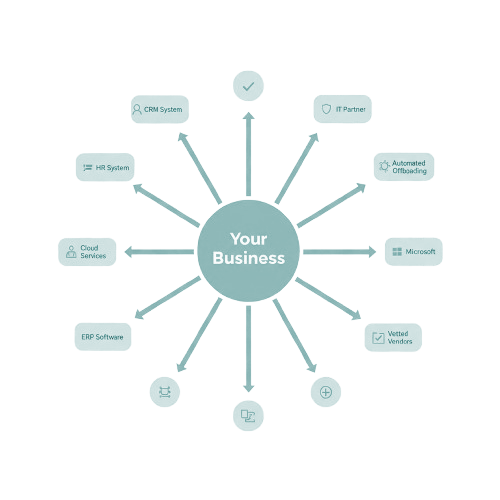
Risk Assessment
Review of current systems and external access to find security gaps or unsafe configurations before they become a problem.
Technical check
Technical deep-dive into your external-facing connections to find weaknesses before they can be exploited by hackers.
Staying Alert
Regular audits to track external parties, manage access rights, and monitor external connections to maintain security and minimise risk.
Questions?
Share your details or book a time to chat online, and we’ll be happy to discuss how our assessments can support your organisation.
We handle your personal data with care and use it only for the purpose for which it was provided. Please read our privacy statement for more information.
* Required


